Security & Trust at BoltPipeline
Your data never leaves your environment. Security, governance, and auditability are core design principles — not add-ons.
TL;DR for Executives
Your data never leaves your environment. BoltPipeline operates using metadata and execution signals only. Pipelines run inside your database, with customer-owned SQL artifacts, full lineage, approval gates, and audit trails. No proprietary runtime. No vendor lock-in.
Six Security Pillars
Built on a zero-trust, boundary-first security model. Every control is part of the architecture.
Boundary-First Design
- No raw data ingestion into the control plane
- No data replication, caching, or external storage
- Only metadata and execution signals leave your environment
- All artifacts are ANSI SQL and customer-owned
Identity & Authentication
- Memory-hard password hashing (Argon2id)
- Multi-Factor Authentication (TOTP)
- Short-lived access tokens (asymmetric)
- Refresh token rotation with replay detection
- Layered brute-force protection
Per-Agent mTLS
- Every agent gets a unique X.509 certificate
- 3-tier PKI hierarchy (Root CA → Intermediate → Agent)
- Full chain validation on every request
- Cryptographically bound to tenant and workload
Access Control & Tollgates
- Role-based access control — Viewer, Developer, Operator, Admin
- Hard approval tollgates between Dev → Integration → Production
- Separation of duties — authors cannot approve their own pipelines
- Re-certification required at every promotion stage
- Full audit trail of approvals with user identity and timestamps
- Pluggable SSO support (roadmap)
Platform Security
- TLS encryption in transit, encryption at rest
- Hardened service-to-service communication
- Least privilege across all services
- Secure defaults with explicit opt-in for elevated capabilities
Compliance & Assurance
- SOC 2 aligned (access control, monitoring, incident response)
- ISO/IEC 27001 aligned risk management
- Clear audit trails and change history
- Incident response and revocation capabilities
Architecture & Isolation
Customer data stays inside your database and network boundary at all times.
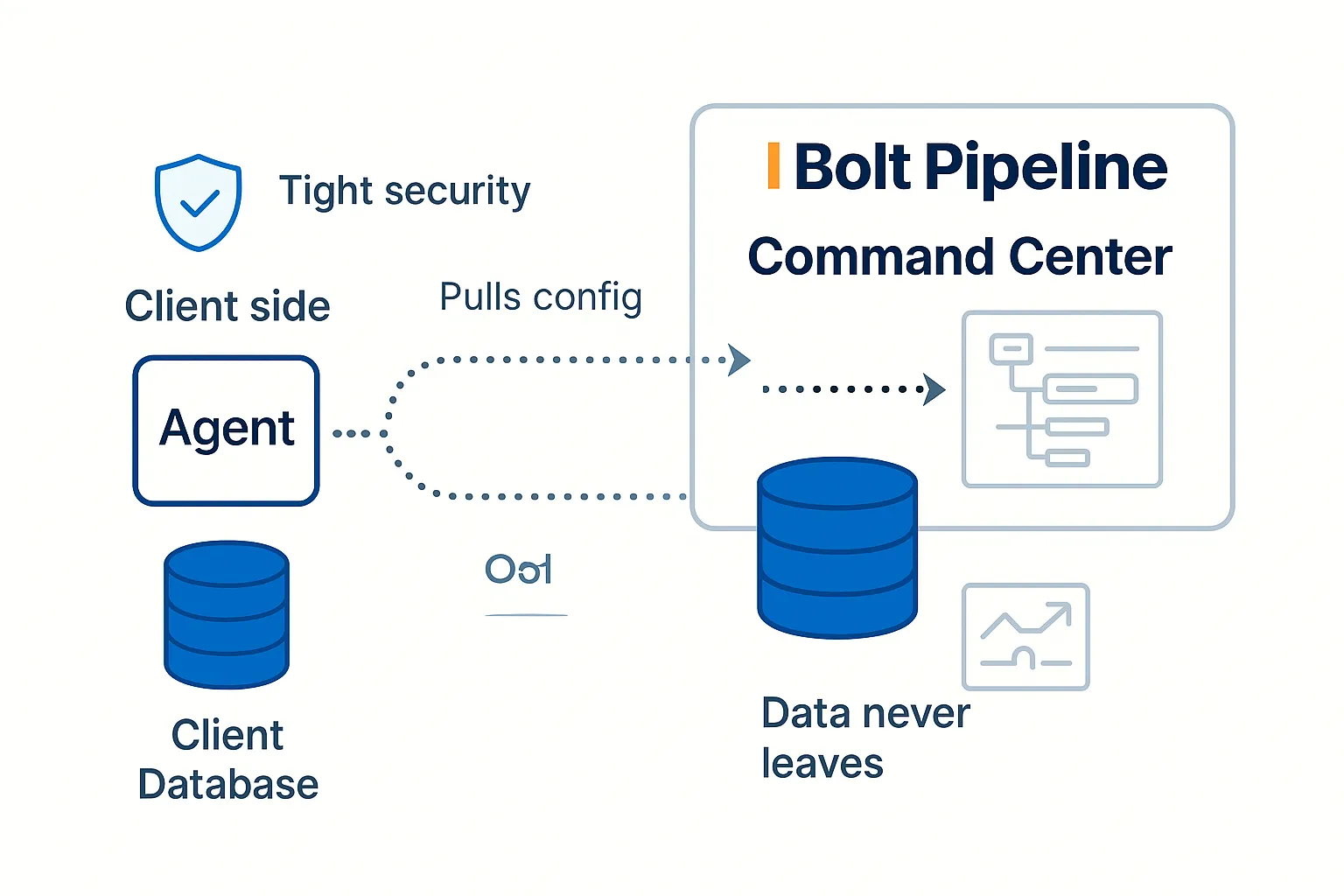
In-Environment Agent
A lightweight Python agent runs inside your infrastructure — your VPC, warehouse, or controlled environment. It executes validations, profiling, and pipeline logic close to the data. Credentials are managed entirely in your environment.
Metadata-Only Control Plane
The Command Center coordinates planning, governance, and visibility using metadata and execution signals only. Table names, column names, schema structure, validation results — never raw row data. Database credentials never collected or transmitted.
What Flows. What Stays.
A clear boundary between what leaves your environment and what never does.
Flows to Command Center
- Table and column names
- Schema metadata (types, constraints)
- SQL text (for compilation)
- Aggregate profiling metrics (counts, %, min/max)
- Validation results
- Execution status signals
Never Leaves Your Environment
- Raw row data
- Database credentials & passwords
- PII content (only match counts returned)
- Query results
- Business data from your tables
- Connection strings or secrets
Transparency & Contact
Trust is built through transparency. If you have questions, need documentation, or want to run a security review, reach out directly.
Detailed security architecture, control mappings, and audit evidence are available under NDA as part of procurement reviews.
security@boltpipeline.ai